HIPAA compliance penalties have reached $40 million in fines since 2016. Healthcare data breaches cost organizations millions while exposing patient information to serious risks. Presence Health discovered this reality in 2017 when they paid $475,000 for violating the Breach Notification Rule.
Healthcare organizations need clear guidance to meet these requirements without overwhelming their teams. This checklist covers essential requirements, implementation steps, and critical pitfalls you must avoid.
CTO2B provides HIPAA-compliant cloud services that simplify regulatory adherence for healthcare organizations. We understand the specific challenges you face when implementing these regulations. Our goal: equip your organization with practical knowledge to achieve compliance while protecting sensitive patient information efficiently.
Key Takeaways
• Conduct thorough risk analysis and implement all three safeguard types: administrative, physical, and technical protections for ePHI
• Train employees regularly on HIPAA policies – over 50% of healthcare workers fail assessments due to inadequate knowledge
• Establish Business Associate Agreements (BAAs) before sharing PHI and maintain proper documentation for at least six years
• Create incident response plans with 60-day breach notification requirements for affected individuals and HHS
• Use automation and HIPAA-compliant tools to reduce human errors and streamline ongoing compliance management
HIPAA compliance extends beyond legal requirements to ethical responsibilities that build patient trust. Organizations must address all eight key requirements comprehensively rather than focusing on isolated components. With proper tools and expertise, compliance becomes manageable, allowing healthcare providers to focus on patient care while maintaining robust data security.
HIPAA Compliance Foundation
The Health Insurance Portability and Accountability Act (HIPAA) created national standards for protecting sensitive patient information across healthcare organizations. Master these fundamentals to build effective compliance programs that protect both patients and your business.
HIPAA Origins and Evolution
HIPAA was enacted in 1996 to solve two critical problems: insurance portability and patient data protection. The original law helped employees maintain coverage between jobs while preventing discrimination based on pre-existing conditions.
Healthcare technology evolution demanded stronger privacy protections. When Congress failed to pass privacy legislation within three years, the Department of Health and Human Services created the HIPAA Privacy Rule. This established the first national framework for health information protection.
The Privacy Rule balances individual privacy with healthcare access needs. The Security Rule adds specific requirements for electronic Protected Health Information (ePHI), demanding administrative, physical, and technical safeguards.
Legal Requirements vs Patient Trust
HIPAA creates both mandatory legal obligations and ethical responsibilities for healthcare organizations. Legal compliance prevents substantial penalties through four core components:
- Privacy Rule – Controls PHI use and disclosure
- Security Rule – Protects electronic PHI with specific safeguards
- Breach Notification Rule – Mandates breach reporting procedures
- Enforcement Rule – Establishes violation penalties and fines
Patient trust extends beyond legal minimums. Protected Health Information (PHI) includes names, Social Security numbers, medical records, treatment plans, and any identifiable patient data. CTO2B recognizes this dual responsibility, our services meet technical requirements while maintaining the ethical standards patients expect from healthcare data handling.
Compliance Scope: Who Must Follow HIPAA
HIPAA applies to covered entities and their business associates with distinct responsibilities for each category.
Covered entities include:
- Healthcare providers transmitting information electronically
- Health plans and insurance companies
- Healthcare clearinghouses processing nonstandard information
Business associates perform PHI-related functions for covered entities:
- IT providers and practice management systems
- Data processing and analysis services
- Legal, accounting, and actuarial firms
- Cloud storage and email encryption providers
Business Associate Agreements (BAAs) formalize these relationships. Covered entities must obtain written safeguard assurances before sharing PHI. The HITECH Act of 2009 made business associates directly liable for HIPAA violations, requiring the same administrative, physical, and technical protections.
Your organization’s HIPAA obligations depend on your role in the healthcare data ecosystem. CTO2B streamlines compliance for both covered entities and business associates through secure, HIPAA-compliant infrastructure solutions that eliminate guesswork from regulatory adherence.
4 Core HIPAA Rules You Must Master
HIPAA compliance centers on four essential rules that control protected health information handling across healthcare organizations. Master these rules to build a solid compliance foundation.
Privacy Rule: Patient Rights and Information Control
The Privacy Rule creates national standards for health information protection while enabling necessary healthcare operations. Patients gain specific rights: examining medical records, requesting corrections, and restricting health plan access to cash-paid treatments.
Protected Health Information (PHI) includes personal identifiers, health conditions, healthcare services, and payment details. Your organization must:
- Notify patients about privacy rights and information usage
- Train staff on privacy procedures
- Designate privacy oversight personnel
- Secure records from unauthorized access
Health plans cannot use genetic information for underwriting under this rule. PHI disclosure is required only when patients request their information or HHS investigates compliance.
Security Rule: Electronic Data Protection
Electronic Protected Health Information (ePHI) receives specific protection through administrative, physical, and technical safeguards. The rule adapts to your organization’s size and structure while maintaining security standards.
Required Protection Areas:
Confidentiality – Unauthorized persons cannot access data
Integrity – Data remains unaltered without authorization
Availability – Authorized users maintain data access
Organizations must:
- Protect against anticipated security threats
- Prevent impermissible uses or disclosures
- Ensure workforce compliance
CTO2B services meet these safeguard requirements, maintaining ePHI security without technical complexity.
Breach Notification Rule: Response Requirements
The HITECH Act established notification requirements for unauthorized PHI disclosures in 2009. Breaches trigger mandatory notifications to affected individuals, HHS, and media when appropriate.
Critical Timeline: 60 days maximum for breach notifications after discovery. Breaches affecting over 500 individuals require media outlet notifications.
Breach assessment factors include:
- PHI type and sensitivity
- Who accessed the information
- Whether data was viewed or retained
- Risk mitigation steps taken
CTO2B automated incident response workflows streamline breach assessment and notification processes.
Enforcement Rule: Penalty Structure
HHS Office for Civil Rights (OCR) enforces civil monetary penalties with tiered violation categories:
Violation Categories:
- Unknowing: $100-$50,000 per violation, $25,000 annual maximum
- Reasonable Cause: $1,000-$50,000 per violation, $100,000 annual maximum
- Willful Neglect (Corrected): $10,000-$50,000 per violation, $250,000 annual maximum
- Willful Neglect (Uncorrected): $50,000 per violation, $1.5 million annual maximum
Penalties increased with August 2024 inflation adjustments. OCR has processed over 374,321 HIPAA complaints since 2003, resolving 99% of cases.
CTO2B compliance solutions protect your organization and patients while establishing privacy and security culture beyond penalty avoidance.
HIPAA Compliance Checklist: Key Requirements
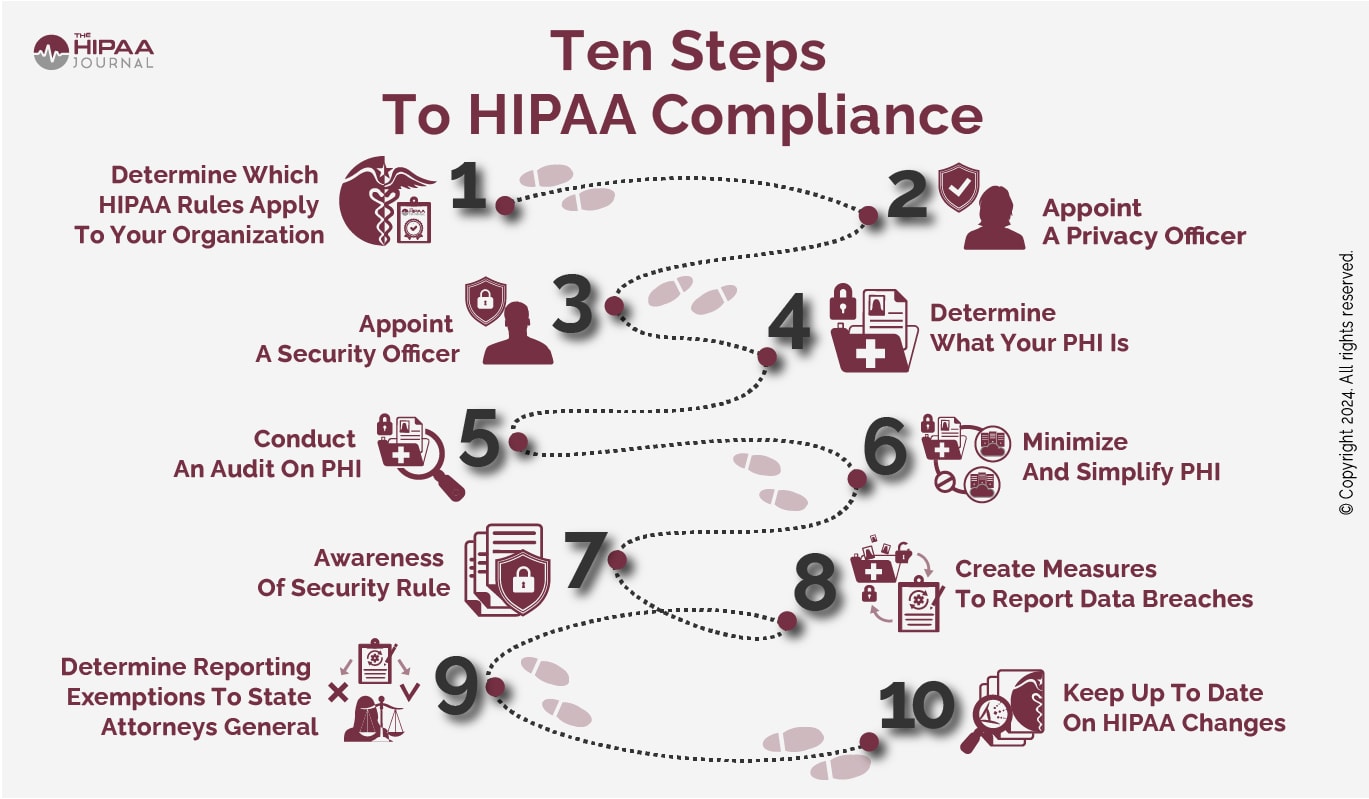
Full HIPAA compliance requires addressing eight critical requirements. Each component protects sensitive patient information while maintaining regulatory adherence.
1. Conduct a full risk analysis
Assess potential risks and vulnerabilities to ePHI. This foundational step identifies threats to confidentiality, integrity, and availability of patient data. Evaluate human, natural, and environmental threats to information systems containing ePHI. Prioritize security measures based on likelihood and potential impact.
2. Implement administrative safeguards
Administrative safeguards comprise over half of HIPAA Security requirements. Designate a Security Officer responsible for implementing policies that prevent, detect, contain, and correct security violations. Develop procedures for supervising workforce members with ePHI access. Deactivate accounts promptly upon termination.
3. Apply physical security controls
Protect buildings, equipment, and systems from unauthorized intrusion and environmental hazards. Implement facility access controls with contingency operations plans. Establish policies for workstation use and security. Control device and media movement containing ePHI.
4. Set up technical safeguards for ePHI
Technical safeguards involve policies and technologies that protect electronic information. Essential implementations include:
- Access controls with unique user identification
- Automatic logoff after periods of inactivity
- Audit controls to track system activity
- Encryption for data at rest and in transit
5. Train employees on HIPAA policies
Provide regular HIPAA training for all workforce members, including management. Training must cover security awareness, phishing and malware threats, suspicious activity recognition, and password management. Schedule annual refresher training.
6. Maintain proper documentation
Document all policies, procedures, and activities related to HIPAA compliance for at least six years. This includes risk assessments, security measures, training records, and BAAs. CTO2B streamlines this documentation process through our HIPAA-compliant management system.
7. Manage business associate agreements (BAAs)
Execute Business Associate Agreements prior to sharing PHI. These contracts establish permissible uses of PHI, require implementation of appropriate safeguards, and mandate reporting of unauthorized disclosures. Extend BAAs to any subcontractors handling PHI.
8. Create an incident response plan
Establish a written, systematic approach for security incident handling. Your plan should outline identification procedures, containment strategies, eradication methods, recovery steps, and notification requirements. Breaches affecting over 500 individuals require notifications within 60 days.
CTO2B offers specialized tools for each requirement, from risk analysis automation to incident response workflows, helping organizations achieve and maintain HIPAA compliance efficiently.
Common HIPAA Violations and How to Avoid Them
Healthcare organizations face predictable compliance challenges that result in costly penalties. Recognizing these violation patterns helps you implement targeted protections.
Improper use or disclosure of PHI
Unauthorized PHI disclosure generates the most HIPAA complaints received by HHS’ Office for Civil Rights. These violations typically stem from careless practices, discussing patient details in public spaces, sending PHI to wrong recipients, or disposing of records improperly. One hospital faced penalties after an employee left a detailed voicemail about a patient’s treatment with their daughter instead of the designated work contact.
Prevention strategies include:
- Apply minimum necessary standards for all communications
- Establish clear PHI disposal procedures
- Require written patient authorization before information sharing
Lack of encryption or access controls
Unencrypted devices create substantial liability exposure. One organization paid $3.2 million in penalties for failing to encrypt portable devices containing PHI. Poor access controls compound these risks by enabling unauthorized PHI access.
Encryption provides essential protection. HIPAA guidelines specify that encrypted PHI breaches aren’t reportable security incidents unless decryption keys are also compromised. CTO2B delivers robust encryption solutions that maintain confidentiality while meeting regulatory requirements.
Failure to notify breaches on time
HIPAA mandates breach notifications without unnecessary delay, within 60 days. Organizations must notify affected individuals, HHS, and media outlets for breaches affecting over 500 people. Many organizations exceed this timeline, triggering substantial penalties.
Inadequate employee training
Over 50% of healthcare employees fail HIPAA assessments. This knowledge gap drives most data breaches, studies show 26% of breaches result from insider carelessness, negligence, or indifference.
Effective training addresses organization-specific policies rather than generic concepts. CTO2B provides targeted training solutions that prepare your staff for real-world scenarios they encounter daily.
HIPAA-Compliant Tools and Services for Full Implementation
Robust HIPAA compliance demands tools that eliminate manual overhead while maintaining security standards. Modern organizations require automated solutions that handle compliance complexities without disrupting daily operations.
Why automation empowers your compliance strategy
Automation reduces HIPAA compliance time and resource requirements by eliminating repetitive manual tasks. Human error causes most violations, automated processes prevent the careless mistakes that lead to costly penalties.
Healthcare organizations face a critical knowledge gap: over 50% of employees fail HIPAA assessments. Automated monitoring systems address this challenge by continuously tracking compliance status and alerting teams to potential issues before violations occur.
CTO2B delivers automated HIPAA compliance
CTO2B provides cloud compliance services that secure sensitive healthcare data while meeting regulatory requirements. Our platform automates ongoing monitoring, protection, and risk management across AWS, Azure, and GCP environments.
Configuration Management: Maintains continuous compliance with evolving regulatory frameworks
Automated Monitoring: Reduces manual effort while ensuring proactive security posture
Risk Assessment: Identifies vulnerabilities before they become compliance violations
Cloud platforms that meet healthcare requirements
HIPAA-compliant telehealth platforms require encryption, authentication protocols, and customizable access controls. Organizations engaging cloud service providers must establish Business Associate Agreements (BAAs) before handling PHI.
End-to-end encryption for data at rest and in transit remains mandatory for any cloud platform supporting HIPAA compliance. CTO2B ensures your cloud infrastructure meets these requirements while optimizing performance and cost efficiency.
Ready to automate your HIPAA compliance? CTO2B handles the technical complexity so you can focus on patient care. Contact us.
Ready to Secure Your Healthcare Data?
Healthcare data breaches continue rising, with penalties now reaching millions of dollars for serious violations. Proactive security measures must replace reactive approaches to data protection.
HIPAA regulations serve an important purpose, protecting patient privacy while enabling necessary information flow. With the right tools and expertise, compliance becomes manageable rather than burdensome.
CTO2B simplifies this process, helping healthcare organizations focus on patient care instead of regulatory complexities. Our HIPAA-compliant cloud solutions ensure your organization meets all requirements efficiently.
Your HIPAA compliance journey demonstrates commitment to patient trust and data security. Contact us to discover how CTO2B can streamline your compliance efforts with our proven healthcare cloud solutions.
FAQs
What are the core components of HIPAA compliance?
HIPAA compliance is built on four main rules: the Privacy Rule, which governs the use and disclosure of protected health information; the Security Rule, which establishes safeguards for electronic PHI; the Breach Notification Rule, which outlines reporting requirements for data breaches; and the Enforcement Rule, which details penalties for non-compliance.
Who needs to comply with HIPAA regulations?
HIPAA regulations apply to two main categories: covered entities (such as healthcare providers, health plans, and healthcare clearinghouses) and their business associates (organizations that perform certain functions involving PHI on behalf of covered entities). Both are required to implement safeguards to protect patient information.
What are some common HIPAA violations and how can they be avoided?
Common violations include improper disclosure of PHI, lack of encryption, failure to report breaches on time, and inadequate employee training. These can be avoided by implementing strict access controls, using encryption for all devices containing PHI, creating a robust incident response plan, and providing comprehensive, regular HIPAA training for all staff members.
How often should HIPAA training be conducted for employees?
While HIPAA doesn’t specify a frequency, best practices suggest conducting HIPAA training annually for all employees. This helps ensure that staff members are up-to-date with the latest regulations and organization-specific policies, reducing the risk of violations due to human error.
How can automation help with HIPAA compliance?
Automation tools can significantly streamline HIPAA compliance by reducing human errors, continuously monitoring compliance status, and alerting organizations to potential issues before they become violations. These tools can help with risk assessments, policy enforcement, access control management, and incident response, making the ongoing compliance process more efficient and effective.
References
[1] – https://compliancy-group.com/what-is-hipaa-compliance/
[2] – https://www.fortinet.com/resources/cyberglossary/hipaa-compliance
[3] – https://www.hhs.gov/hipaa/for-professionals/security/laws-regulations/index.html
[4] – https://www.cdc.gov/phlp/php/resources/health-insurance-portability-and-accountability-act-of-1996-hipaa.html
[5] – https://www.hipaajournal.com/purpose-of-hipaa/
[6] – https://www.hhs.gov/hipaa/for-professionals/privacy/laws-regulations/index.html
[7] – https://www.jandonline.org/article/S2212-2672(20)31501-X/fulltext
[8] – https://www.hhs.gov/hipaa/for-professionals/privacy/guidance/business-associates/index.html
[9] – https://www.hhs.gov/hipaa/for-professionals/covered-entities/index.html
[10] – https://www.hipaajournal.com/differences-hipaa-business-associate-hipaa-covered-entity/
[11] – https://www.cms.gov/files/document/mln909001-hipaa-basics-providers-privacy-security-breach-notification-rules.pdf
[12] – https://www.hhs.gov/hipaa/for-professionals/security/index.html
[13] – https://www.hipaajournal.com/hipaa-explained/
[14] – https://www.hhs.gov/hipaa/for-professionals/breach-notification/breach-reporting/index.html
[15] – https://www.ama-assn.org/practice-management/hipaa/hipaa-breach-notification-rule
[16] – https://www.ama-assn.org/practice-management/hipaa/hipaa-violations-enforcement
[17] – https://www.hipaajournal.com/what-are-the-penalties-for-hipaa-violations-7096/
[18] – https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/data/enforcement-highlights/index.html
[19] – https://www.hhs.gov/hipaa/for-professionals/security/guidance/guidance-risk-analysis/index.html
[20] – https://www.hhs.gov/sites/default/files/ocr/privacy/hipaa/administrative/securityrule/adminsafeguards.pdf
[21] – https://www.hipaajournal.com/hipaa-risk-assessment/
[22] – https://www.hhs.gov/sites/default/files/ocr/privacy/hipaa/administrative/securityrule/physsafeguards.pdf
[23] – https://www.clarity-ventures.com/glossary/physical-safeguards
[24] – https://www.hhs.gov/sites/default/files/ocr/privacy/hipaa/administrative/securityrule/techsafeguards.pdf
[25] – https://www.hipaajournal.com/hipaa-technical-safeguards/
[26] – https://www.hhs.gov/hipaa/for-professionals/training/index.html
[27] – https://www.hipaajournal.com/hipaa-training-requirements/
[28] – https://sprinto.com/blog/hipaa-documentation/
[29] – https://www.hhs.gov/hipaa/for-professionals/covered-entities/sample-business-associate-agreement-provisions/index.html
[30] – https://www.hipaajournal.com/hipaa-business-associate-agreement/
[31] – https://www.hhs.gov/sites/default/files/cybersecurity-incident-response-plans.pdf
[32] – https://compliancy-group.com/hipaa-cyber-incident-response-requirements/
[33] – https://www.hipaajournal.com/employees-prevent-hipaa-violations/
[34] – https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/examples/all-cases/index.html
[35] – https://www.hipaajournal.com/common-hipaa-violations/
[36] – https://www.hipaajournal.com/hipaa-encryption-requirements/
[37] – https://www.hhs.gov/hipaa/for-professionals/breach-notification/index.html
[38] – https://www.medicaleconomics.com/view/more-than-half-of-employees-don-t-understand-hipaa-rules
[39] – https://hipaatimes.com/how-to-avoid-comming-hipaa-violations-in-digital-communications
[40] – https://secureframe.com/hub/hipaa/cost-and-time-savings
[41] – https://community.trustcloud.ai/docs/grc-launchpad/grc-101/compliance/the-benefits-of-compliance-automation-in-the-healthcare-industry/
[42] – https://cto2b.io/solutions/cloud-compliance/
[43] – https://www.fortinet.com/resources/articles/hipaa-compliant-telehealth-platforms
[44] – https://www.hhs.gov/hipaa/for-professionals/special-topics/health-information-technology/cloud-computing/index.html
[45] – https://www.cerberusftp.com/blog/best-practices-in-hipaa-compliant-data-and-file-transfer/